US, Germany and Canada Dismantle Major Botnet Network Behind Massive DDoS Attacks
Authorities in the United States, Germany and Canada have dismantled infrastructure linked to four major botnets that infected more than three million devices worldwide, in one of the most significant recent crackdowns on IoT-powered cyberattacks. The networks, identified as Aisuru, KimWolf, JackSkid and Mossad, were used to launch distributed denial-of-service attacks against targets around the world, including systems tied to the US Department of Defense.
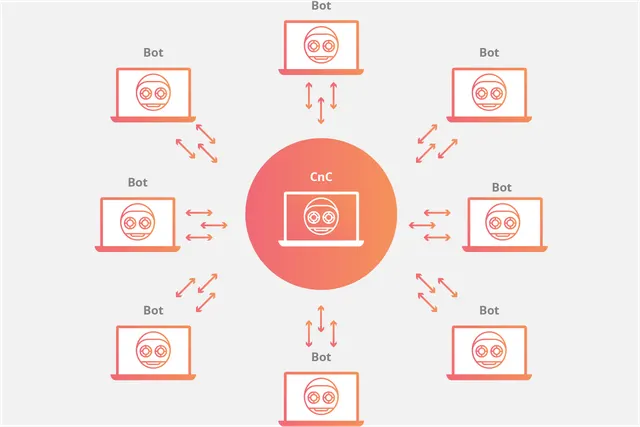
The operation, announced by the US Department of Justice, reflects a growing international push to disrupt not just individual cybercriminals but the infrastructure that makes large-scale attacks possible. Investigators said the botnets had quietly absorbed millions of internet-connected devices, turning everyday hardware into attack tools for hire.

Millions of hijacked IoT devices formed the backbone of the attacks
According to the Justice Department, most of the infected systems were Internet of Things devices such as webcams, digital video recorders and Wi-Fi routers. These products are often deployed with weak default settings, outdated firmware or minimal monitoring, which makes them attractive targets for botnet operators looking to build massive, low-cost attack networks.
Once compromised, the devices were used to flood victims with malicious traffic. Court documents cited in reporting indicate the four botnets collectively issued hundreds of thousands of DDoS attack commands. Some victims were also hit with extortion demands, adding a criminal revenue stream on top of the disruption itself.
The scale is striking. Reuters reported that more than three million devices were affected globally, including hundreds of thousands in the United States alone. That kind of footprint gives operators the ability to unleash outsized traffic floods without relying on traditional server infrastructure.
Defense-related targets were in the firing line
The Justice Department said some of the attacks were directed at IP addresses owned by the Department of Defense Information Network. That puts the campaign in a more serious category than routine criminal disruption. Even when DDoS attacks do not penetrate networks, they can still strain public-facing systems, interrupt services and force organizations to spend heavily on mitigation and recovery.
Kenneth DeChellis, a special agent in charge at the Department of Defense Investigative Service, said the disruption highlights a commitment to eliminating cyber threats aimed at the department and its personnel. The statement underlines how botnet abuse is no longer just a nuisance problem for websites and gaming platforms, but a national security concern when military systems or defense infrastructure are drawn into the target list. }
The investigation also exposed how botnets are evolving
Beyond brute-force traffic floods, investigators said at least some of the infected devices were repurposed as residential proxies, allowing third parties to route internet traffic through unwitting victims’ home networks. Reuters reported that the KimWolf botnet in particular was tied to this kind of abuse, showing how modern botnets are increasingly used for multiple criminal services at once.
That evolution matters. A compromised webcam or router may now serve as a DDoS node one day and as anonymized proxy infrastructure the next. For defenders, that broadens the risk from temporary service disruption to sustained abuse of consumer and small business networks.
Wired also reported that these botnets were associated with some of the most intense recent traffic floods, with one related attack reaching 31.4 terabits per second. Whether or not every campaign tied to this infrastructure reached that scale, the operation underscores how deeply Mirai-style tactics have evolved from basic IoT exploitation into industrialized cybercrime.
A coordinated international disruption effort
The operation was carried out simultaneously across the United States, Germany and Canada and targeted individuals believed to be behind the infrastructure. German authorities searched the homes of suspects in Germany and Canada, and seized storage devices as well as cryptocurrency worth tens of thousands of dollars, according to Reuters.
The public and private sectors worked side by side. The Justice Department said nearly two dozen technology companies assisted, including Amazon Web Services, Google, PayPal and Nokia. Europol’s PowerOFF team, which has focused on DDoS-related cybercrime since 2017, also supported the operation.
That cooperation is becoming a standard feature of large cyber takedowns. Law enforcement can seize domains and infrastructure, but cloud providers, network operators, payment services and platform companies often hold the telemetry needed to map how the ecosystems function in practice.
Why this matters for defenders
The takedown is a win, but not a final one. Botnets built from poorly secured IoT devices remain relatively easy to rebuild, especially when vendors and users fail to patch firmware, change default passwords or retire unsupported hardware. As long as vulnerable routers, DVRs and cameras remain exposed online, the supply of potential bots remains steady.
For enterprises and public-sector teams, the lesson is simple. DDoS defense is no longer just about absorbing traffic spikes. It also means inventorying internet-facing devices, hardening remote management paths, monitoring unusual outbound traffic and working with providers that can detect botnet-related patterns early. The disruption of Aisuru, KimWolf, JackSkid and Mossad may buy time, but it does not remove the structural weaknesses that made them possible.
