Microsoft Warns of Code of Conduct Phishing Campaign Using AiTM to Steal Authentication Tokens
A compliance-themed email is easy to ignore until it accuses the recipient of being part of an internal conduct review. That pressure point is exactly what this campaign abused.
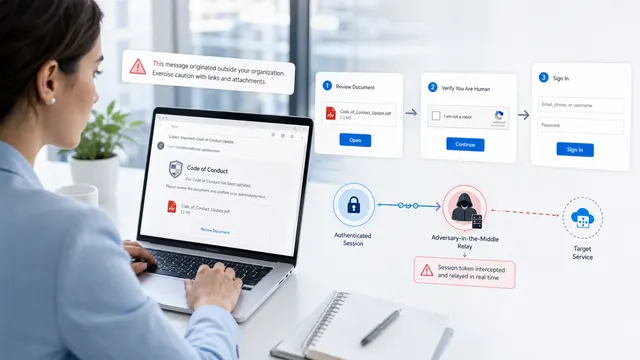
Microsoft says attackers ran a multi-stage “code of conduct” phishing operation that targeted more than 35,000 users across over 13,000 organizations in 26 countries between April 14 and April 16, 2026. The campaign was not built around crude credential harvesting. It moved victims through PDF attachments, CAPTCHA challenges, staging pages, and finally an adversary-in-the-middle authentication flow designed to capture tokens and gain account access.
What Happened
According to Microsoft Defender Research, the phishing waves ran between 06:51 UTC on April 14 and 03:54 UTC on April 16, 2026. The United States accounted for 92% of observed targets, while the most affected sectors included healthcare and life sciences at 19%, financial services at 18%, professional services at 11%, and technology and software at 11%.
The lure was built around internal compliance pressure. Emails used display names such as “Internal Regulatory COC,” “Workforce Communications,” and “Team Conduct Report.” Subject lines included “Internal case log issued under conduct policy” and “Reminder: employer opened a non-compliance case log.”
The message body claimed that a code of conduct review had been opened and instructed recipients to review a personalized attachment. Microsoft noted that the emails included organization-specific references and authenticity language stating that the message had been issued through an authorized internal channel. The campaign also used a green banner claiming the content had been encrypted using Paubox, a legitimate service associated with HIPAA-compliant communications.
The Attack Chain
The emails carried PDF attachments with names such as “Awareness Case Log File – Tuesday 14th, April 2026.pdf” and “Disciplinary Action – Employee Device Handling Case.pdf.” Inside the PDF, victims were directed to click a “Review Case Materials” link.
That link sent users to attacker-controlled infrastructure, including domains such as acceptable-use-policy-calendly[.]de and compliance-protectionoutlook[.]de. The first stage displayed a Cloudflare CAPTCHA, likely to block automated scanners and sandbox analysis while making the interaction feel more legitimate.
After completing the CAPTCHA, victims moved to an intermediate site that claimed the requested documentation was encrypted and required account authentication. Microsoft said this stage had some hallmarks of device code phishing, although the company could only confirm the adversary-in-the-middle portion of the attack chain.
The campaign then asked users to enter their email address, complete a second image-selection CAPTCHA, and proceed to a final page claiming that the code of conduct materials had been securely logged and time-stamped. Victims were then prompted to schedule a meeting and sign in with Microsoft.
That final “Sign in with Microsoft” step initiated the real damage: an adversary-in-the-middle session hijacking flow. Instead of merely stealing usernames and passwords, the attackers attempted to proxy the authentication session and capture tokens that could provide immediate access to compromised accounts.
Why This Stands Out
The campaign matters because it combines several trends defenders are already seeing separately: polished workplace-themed lures, trusted-looking delivery infrastructure, CAPTCHA-gated phishing, PDF-based redirection, and token theft.
The social engineering was deliberately uncomfortable. A code of conduct accusation creates urgency without needing a financial pretext or executive impersonation. It pressures employees to act quickly, privately, and emotionally. That makes it especially dangerous in environments where users have been trained to treat compliance and HR communications as mandatory.
The technical structure also shows why traditional phishing controls are under pressure. CAPTCHA gates can reduce automated visibility. PDF links can shift the malicious URL away from the email body. AiTM infrastructure can bypass non-phishing-resistant MFA by capturing session tokens after authentication has already succeeded.
Why Defenders Should Care
This is not just another phishing campaign. It is a reminder that MFA alone is not a finish line when the authentication method is still phishable.
AiTM phishing does not need to defeat the identity provider directly. It inserts itself into the sign-in path, proxies the session, and captures reusable authentication material. Once attackers have a valid session token, they may be able to access cloud resources without needing the victim’s password again.
For security teams, the detection surface should include more than email telemetry. Suspicious URL clicks, unusual sign-in properties, anomalous tokens, impossible travel activity, unfamiliar session cookie behavior, and post-delivery email removals all matter in this type of campaign.
Microsoft-Recommended Defensive Actions
Microsoft advised organizations to review Exchange Online Protection and Microsoft Defender for Office 365 settings, enable Zero-hour auto purge, use Safe Links and Safe Attachments, and manually hunt for messages with similar sender addresses, URLs, or subject fields.
Microsoft also recommended enabling network protection in Microsoft Defender for Endpoint, encouraging browsers that support Microsoft Defender SmartScreen, and moving accounts toward passwordless or phishing-resistant authentication methods such as Windows Hello and FIDO security keys. Conditional Access policies should be scoped carefully for privileged accounts, especially where phishing-resistant MFA is available.
Indicators of Compromise
The following indicators were published by Microsoft in relation to this campaign.
| Indicator | Type | Description | First Seen | Last Seen |
|---|---|---|---|---|
| compliance-protectionoutlook[.]de | Domain | Domain hosting malicious campaign content | 2026-04-14 | 2026-04-16 |
| acceptable-use-policy-calendly[.]de | Domain | Domain hosting malicious campaign content | 2026-04-14 | 2026-04-16 |
| cocinternal[.]com | Domain | Domain hosting sender email address | 2026-04-14 | 2026-04-16 |
| Gadellinet[.]com | Domain | Domain hosting sender email address | 2026-04-14 | 2026-04-16 |
| Harteprn[.]com | Domain | Domain hosting sender email address | 2026-04-14 | 2026-04-16 |
| Cocpostmaster[@]cocinternal.com | Email address | Email address used to send campaign emails | 2026-04-14 | 2026-04-16 |
| Nationaladmin[@]gadellinet.com | Email address | Email address used to send campaign emails | 2026-04-14 | 2026-04-16 |
| Nationalintegrity[@]harteprn.com | Email address | Email address used to send campaign emails | 2026-04-14 | 2026-04-16 |
| M365premiumcommunications[@]cocinternal.com | Email address | Email address used to send campaign emails | 2026-04-14 | 2026-04-16 |
| Documentviewer[@]na.businesshellosign.de | Email address | Email address used to send campaign emails | 2026-04-14 | 2026-04-16 |
| Awareness Case Log File – Monday 13th, April 2026.pdf | Filename | Name of PDF attachment containing phishing link | 2026-04-14 | 2026-04-14 |
| Awareness Case Log File – Tuesday 14th, April 2026.pdf | Filename | Name of PDF attachment containing phishing link | 2026-04-15 | 2026-04-15 |
| Awareness Case Log File – Wednesday 15th, April 2026.pdf | Filename | Name of PDF attachment containing phishing link | 2026-04-16 | 2026-04-16 |
| 5DB1ECBBB2C90C51D81BDA138D4300B90EA5EB2885CCE1BD921D692214AECBC6 | SHA-256 | File hash of campaign PDF attachment | 2026-04-14 | 2026-04-16 |
| B5A3346082AC566B4494E6175F1CD9873B64ABE6C902DB49BD4E8088876C9EAD | SHA-256 | File hash of campaign PDF attachment | 2026-04-14 | 2026-04-16 |
| 11420D6D693BF8B19195E6B98FEDD03B9BCBC770B6988BC64CB788BFABE1A49D | SHA-256 | File hash of campaign PDF attachment | 2026-04-14 | 2026-04-16 |
Detection Notes
Microsoft listed several relevant Defender detections for this activity, including potentially malicious URL clicks, user click-throughs to malicious URLs, suspicious email sending patterns, email messages removed after delivery, user-reported phishing, anomalous tokens, unfamiliar sign-in properties, unfamiliar sign-in properties for session cookies, and impossible travel activity.
For hunting, Microsoft also published sender addresses linked to the campaign, including cocpostmaster[@]cocinternal.com, nationaladmin[@]gadellinet.com, nationalintegrity[@]harteprn.com, m365premiumcommunications[@]cocinternal.com, and documentviewer[@]na.businesshellosign.de.
NeuraCyb's Assessment
The most important lesson from this campaign is that attackers are no longer relying on users to simply hand over passwords. They are building believable workflows that walk victims into real authentication experiences and then steal the session. For defenders, the priority is clear: reduce exposure to phishable MFA, inspect the full redirect chain, and treat polished internal-policy emails with the same suspicion once reserved for obvious credential theft.
References
- Microsoft Security Blog: Breaking the code: Multi-stage ‘code of conduct’ phishing campaign leads to AiTM token compromise
- Microsoft Learn: Recommended settings for Exchange Online Protection and Microsoft Defender for Office 365
- Microsoft Learn: Zero-hour auto purge in Microsoft Defender for Office 365
- Microsoft Learn: Network protection in Microsoft Defender for Endpoint
- Microsoft Learn: Authentication methods in Microsoft Entra ID
