DarkSword iPhone Spyware Exposes Millions of Devices to One-Click Data Theft

A newly disclosed iPhone spyware framework known as DarkSword has sharpened concerns around mobile security after researchers said it was used in real-world attacks against Apple devices through booby-trapped websites. The exploit chain does not rely on a user installing an app or opening a suspicious attachment. In many cases, simply landing on a compromised page is enough to trigger the attack on vulnerable devices.
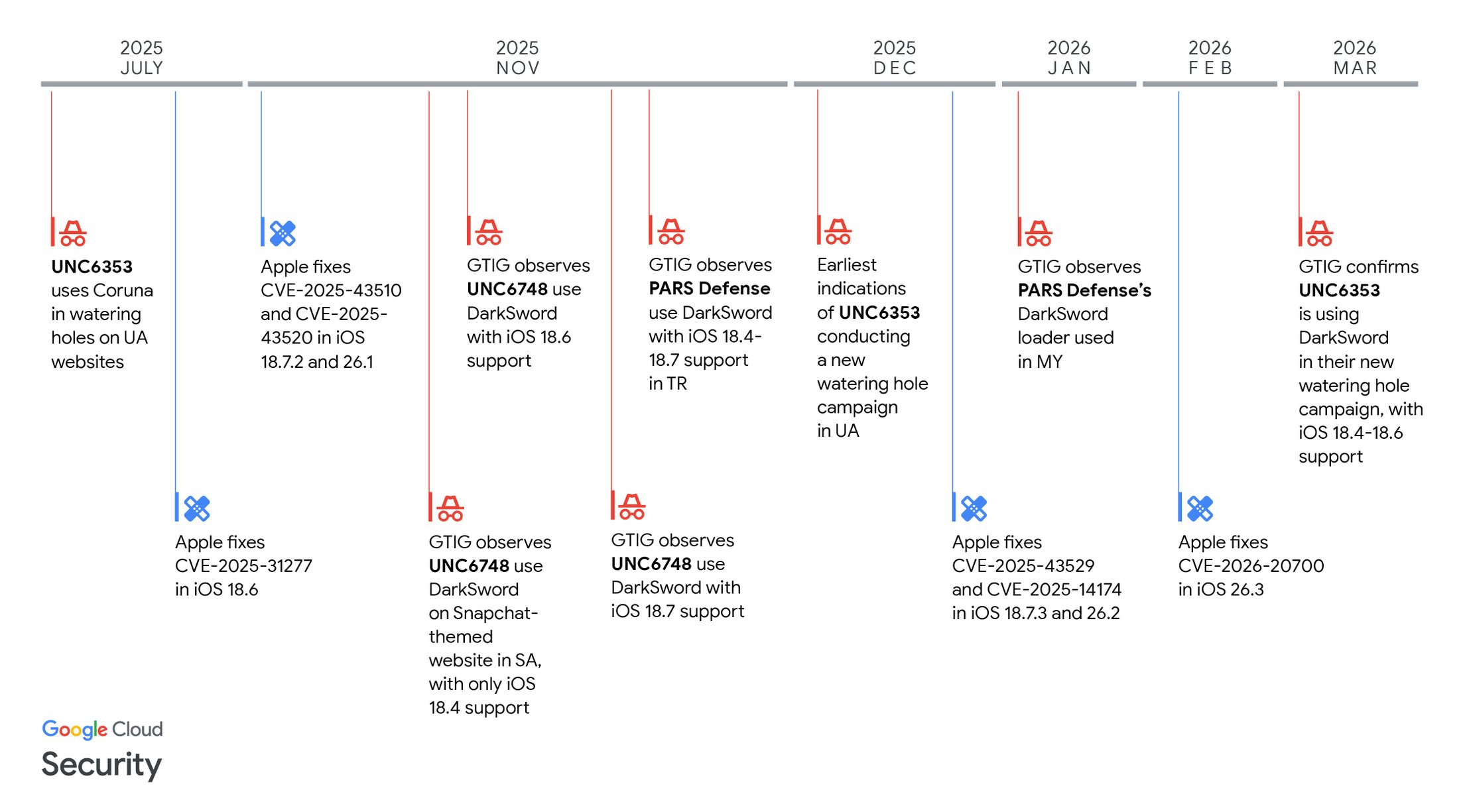
The campaign has drawn attention because of both its reach and its method. Researchers from Google Threat Intelligence Group, Lookout, and iVerify said DarkSword was observed in multiple operations tied to different threat actors, including campaigns targeting users in Ukraine and earlier activity aimed at users in Saudi Arabia. That points to something bigger than a one-off espionage toolkit. It suggests a growing market for reusable iPhone exploitation infrastructure.
Why DarkSword has become a major concern
What makes DarkSword especially alarming is that it appears built for speed. Instead of planting long-term spyware and lingering on a phone for days or weeks, the malware is designed to get in, pull data out, and disappear. Researchers describe it as a hit-and-run operation, with dwell time that may last only minutes depending on how much information is found and exfiltrated.
That short window matters. Once the device is restarted, traces of the attack can become far harder to spot. For defenders, that means traditional assumptions around persistence and forensic recovery do not always apply. A victim may never realize the compromise took place, even after sensitive data has already been siphoned away.
The exposed versions are not obscure legacy builds. Researchers said DarkSword supported iOS 18.4 through 18.7, while field investigations in Ukraine specifically pointed to devices running iOS 18.4 through 18.6.2. Security firms have estimated that roughly 220 million to 270 million iPhones may still be running vulnerable, unpatched software versions, making this one of the more consequential recent mobile threat disclosures.
What attackers can steal from an infected iPhone
DarkSword is not limited to one class of information. According to the technical analyses, the payloads were capable of extracting a broad range of highly personal and operationally sensitive data from a compromised device.
That includes call logs, contacts, calendars, notes, photos, screenshots, browsing history, account identities, SIM information, location data, Wi-Fi credentials, and iCloud-related content. Researchers also said the toolkit was capable of accessing messaging and communication data from services such as iMessage, email, WhatsApp, and Telegram.
Perhaps most worrying for some users, the compromise can extend to financial information and cryptocurrency wallet credentials. That expands the threat beyond classic surveillance. DarkSword sits at the uncomfortable intersection of espionage tooling, cybercrime opportunity, and mass exploitation.
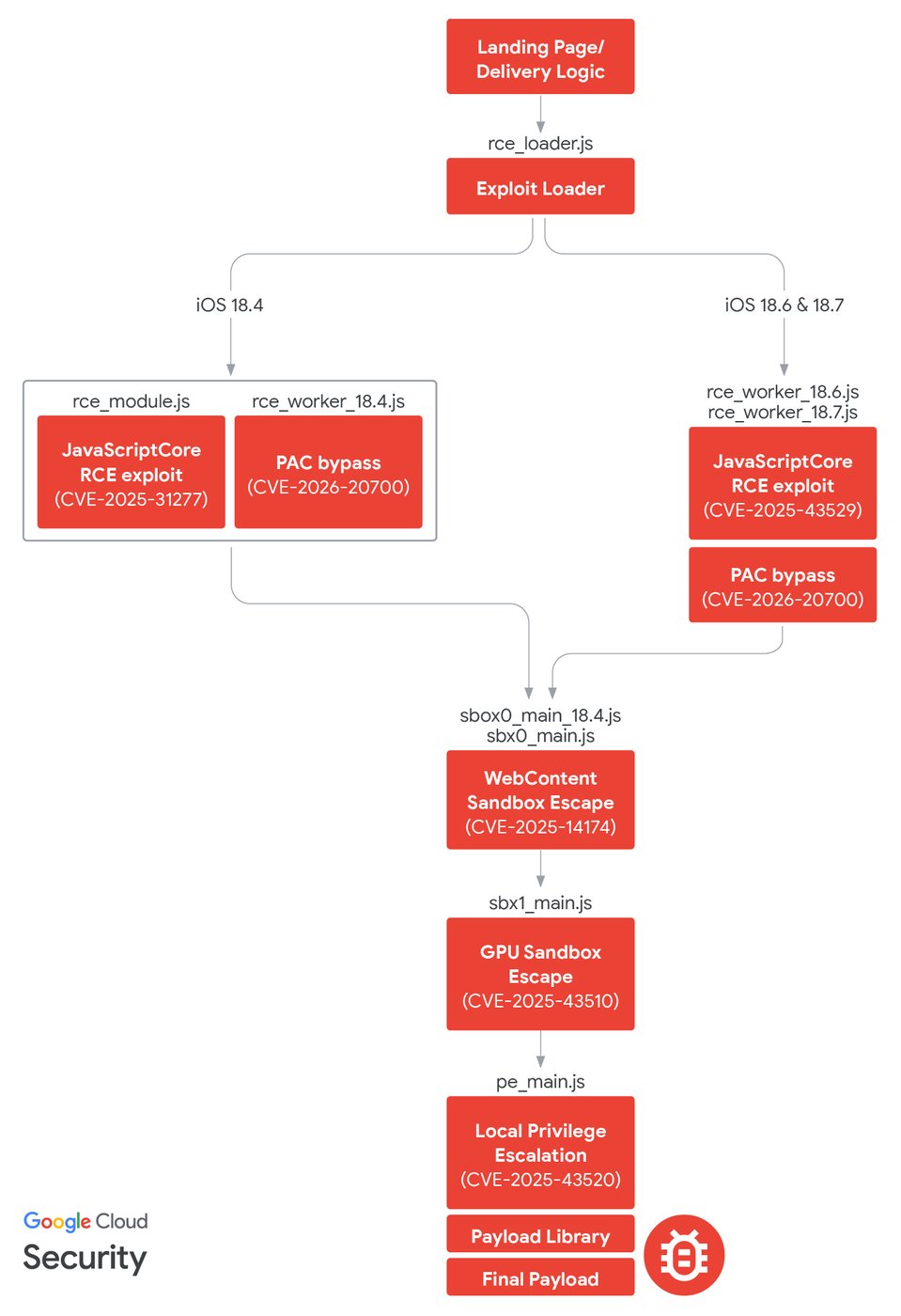
How the attacks were delivered
In one of the clearest examples, researchers said DarkSword was delivered through compromised legitimate websites in Ukraine. Users visiting those sites from vulnerable iPhones could be silently pushed into the exploit chain through malicious iframes and Safari-focused delivery logic. In practical terms, the website looked normal while the attack unfolded behind the scenes.
Earlier activity followed a similar deception model. Google said one campaign used a Snapchat-themed decoy site, designed to appear harmless while routing eligible targets into the attack flow. In another case, threat actors are believed to have compromised official and news-related Ukrainian websites, turning trusted online destinations into launch pads for mobile exploitation.
This technique, often described as a watering hole attack, remains effective because it does not always require tricking the user into downloading anything. It weaponises trust instead. The victim visits a familiar site, and the phone does the rest.
A sign of a wider mobile exploit market
DarkSword is significant not only because of what it can do, but because of who appears to be using it. Google said the exploit chain was observed in the hands of multiple actors, including suspected state-backed operators and commercial surveillance vendors. That suggests the underlying capability is being shared, sold, or repurposed across different customers and missions.
The overlap with the previously disclosed Coruna toolkit deepens that concern. Researchers linked DarkSword infrastructure to servers previously associated with Coruna, another exploit chain used against older iOS versions. The pattern increasingly looks less like isolated research-grade intrusion and more like an emerging ecosystem for advanced iPhone compromise.
There is also an unusual bluntness to the operations. Researchers noted that some of the code and operational choices appeared sloppy by the standards of top-tier covert espionage campaigns. That may indicate the operators were less worried about burning the exploit, possibly because they believed replacement tooling would follow.
What Apple users should do now
Apple has already addressed the underlying vulnerabilities through security updates, and malicious domains identified by Google have been blocked through Safari protections. Even so, the gap between patch release and user adoption remains the real problem. Mobile threats like DarkSword thrive in that window.
For iPhone users, the most important step is straightforward: update immediately to the latest available iOS version. Users who cannot update right away, especially those at elevated risk such as journalists, government personnel, executives, activists, and people operating in sensitive regions, should consider enabling Lockdown Mode for additional protection.
DarkSword is also a reminder that mobile devices now sit firmly on the front line of cyber operations. Phones carry identity, communications, finance, travel, and work in one place. That concentration of value is exactly why advanced attackers keep returning to them and why the old assumption that phones are safer by default is becoming harder to defend.
