Critical Microsoft SharePoint Flaw CVE-2026-20963 Now Exploited in Attacks, CISA Warns

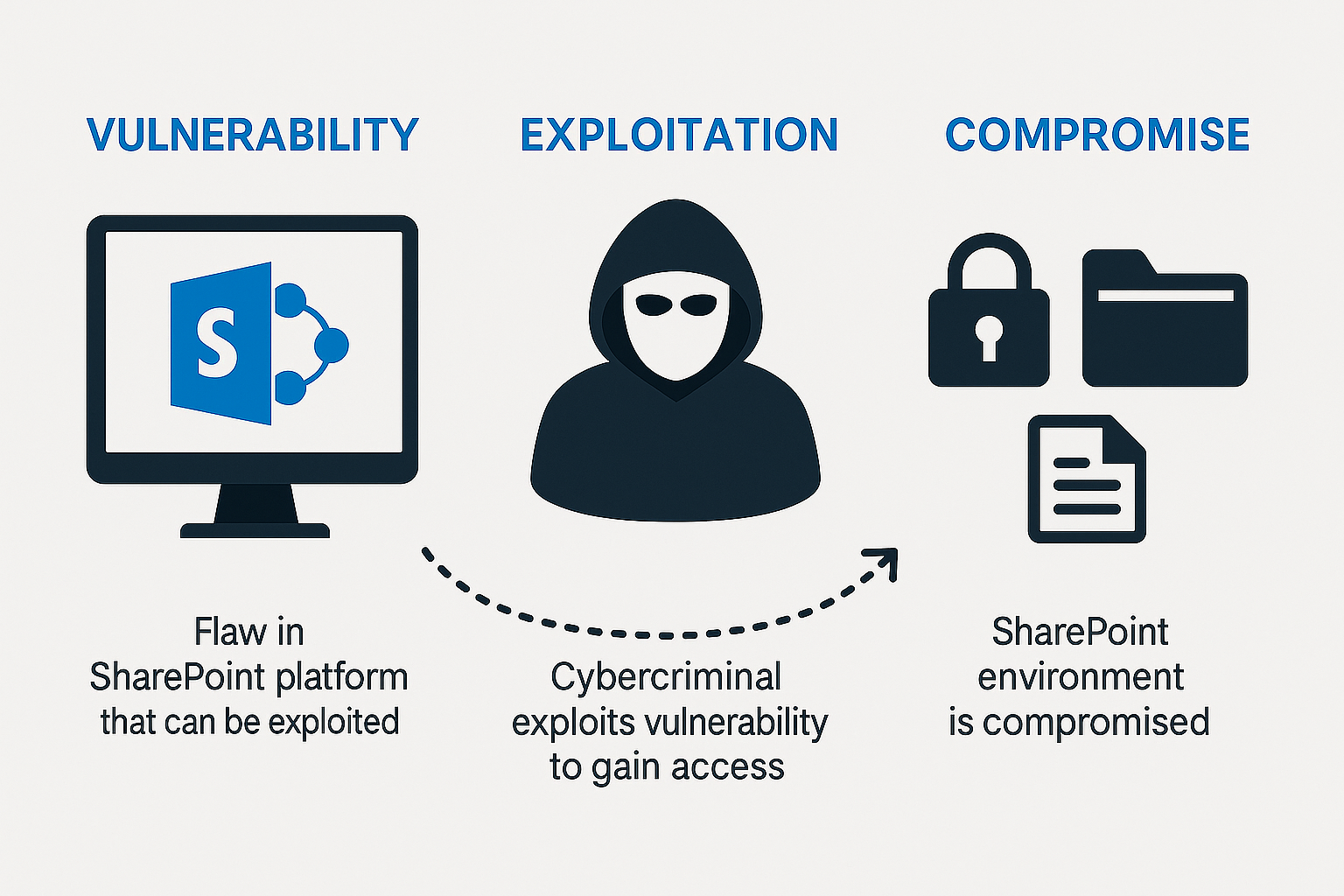
Microsoft SharePoint is again under scrutiny after U.S. authorities confirmed active exploitation of CVE-2026-20963, a critical vulnerability that can open the door to remote code execution on exposed and unpatched servers. The flaw had already been fixed earlier this year, but its addition to CISA’s Known Exploited Vulnerabilities catalog has transformed it from a patching priority into an urgent incident-response issue.
The warning lands at a sensitive moment for enterprise defenders. SharePoint remains widely used for internal collaboration, document storage and workflow automation, especially in large organizations and government environments. When a vulnerability in that stack moves from theoretical risk to active exploitation, the security conversation changes immediately.
That is exactly what has happened here. Federal agencies have been told to act quickly, and private organizations are being urged to do the same. For many defenders, the more uncomfortable question is no longer whether the flaw is dangerous, but whether exposed SharePoint environments were already scanned, probed or compromised before patching caught up.
What CVE-2026-20963 does and why it matters
CVE-2026-20963 is a deserialization of untrusted data vulnerability in Microsoft SharePoint. In practical terms, this type of weakness can allow attackers to feed malicious data into a vulnerable application in a way that results in code execution on the target server.
That makes the flaw especially severe because SharePoint often sits close to business-critical information. It may contain internal documents, project data, workflow logic, sensitive records and connections to other enterprise systems. A successful exploit against SharePoint is rarely just about one server. It can become an entry point into a much broader environment.
Public reporting on Microsoft’s original advisory said successful exploitation could allow an unauthenticated attacker in a network-based attack to write arbitrary code and execute it remotely on the SharePoint Server. Even where technical wording differs across advisory sources, the operational message is clear enough: defenders should treat this as a high-consequence server-side compromise risk.
The affected SharePoint versions put pressure on on-premises defenders
The versions most prominently tied to the warning are SharePoint Enterprise Server 2016, SharePoint Server 2019 and SharePoint Server Subscription Edition. These are not obscure products running only in forgotten labs. They are common in real production environments, including networks where legacy dependencies and change-control friction often delay patch deployment.
That matters because on-premises collaboration infrastructure tends to accumulate complexity over time. A SharePoint server may be integrated with identity systems, file repositories, internal portals, business apps and customized workflows. Patching is rarely just a quick restart. In some organizations, it requires maintenance windows, testing and coordination across multiple teams.
Unfortunately, attackers do not wait for change boards. Once public awareness rises around a critical vulnerability and exploitation begins, scanning activity tends to follow. Security teams that were already running lean now have to assess exposure, confirm patch status, review logs, check for suspicious activity and validate whether internet-facing SharePoint assets are truly locked down.
Why CISA’s KEV listing changes the urgency
CISA does not add flaws to its Known Exploited Vulnerabilities catalog casually. A KEV listing means there is evidence that attackers are using the vulnerability in the wild. That changes how defenders, regulators and leadership teams should think about risk.
For federal civilian agencies, the response is mandatory. CISA ordered them to remediate CVE-2026-20963 by March 21. That is a narrow deadline, and it reflects the seriousness of the exploitation signal. In the private sector, there may be no federal directive, but the practical expectation is similar. Patch, mitigate, isolate or accept a growing compromise risk.
The KEV process also matters because it helps security teams cut through patch fatigue. Enterprises face hundreds of disclosed vulnerabilities every month, and most do not become top-tier priorities. When a flaw lands in KEV, it is one of the clearest signals available that remediation should move to the front of the queue.
A patch existed in January, but delayed remediation creates the real window
One of the recurring patterns in modern enterprise security is that the most damaging exploitation often happens after a fix is already available. CVE-2026-20963 was patched by Microsoft in January, yet organizations still face risk in March because not every environment is patched on time.
There are many reasons for that lag. Some organizations struggle with asset visibility. Others are caught between operational stability and security urgency. In certain environments, older SharePoint implementations remain deeply embedded in business processes, which can make updates feel risky even when not updating is riskier still.
But once active exploitation begins, those trade-offs become harder to defend. A missed patch is no longer a theoretical governance issue. It becomes a live exposure with the potential to trigger incident response, containment work, restoration costs and executive scrutiny.
Older and unsupported deployments may face an even harder choice
The warning is especially uncomfortable for organizations that still rely on end-of-support SharePoint versions. Systems outside mainstream support often remain in use because they back critical workflows, support long-lived custom applications or sit in environments where modernization has been deferred year after year.
That creates a painful reality. If a product is no longer supported, defenders may not have a viable patch path. In that situation, the security options become more disruptive: isolate the service, restrict access aggressively, place it behind compensating controls, or move toward decommissioning. CISA’s general guidance in these cases is blunt for a reason. If you cannot secure an exposed vulnerable product, you may need to stop using it.
This is one reason vulnerabilities in collaboration and content platforms tend to trigger outsized concern. These are not always simple standalone servers. They are often deeply entangled with line-of-business processes, identity flows and institutional habits built over many years.
The separate Zimbra warning shows a broader pattern
CISA’s alert did not stop with SharePoint. The agency also flagged an actively exploited Zimbra Collaboration Suite flaw, identified as CVE-2025-66376, a stored cross-site scripting weakness affecting the Classic UI. That issue carries a later federal remediation deadline, but its inclusion alongside the SharePoint flaw sends a broader message.
Attackers continue to target enterprise collaboration and messaging platforms because they are rich in access, trust and business value. Email suites, document portals and workflow systems sit close to users, sensitive content and administrative functions. Compromising them can yield persistence, data access and a stepping stone into adjacent systems.
In other words, this is not just about one SharePoint CVE. It is part of a wider pressure pattern on the software layers organizations rely on every day to communicate, share files and keep work moving.
What defenders should do now
Organizations running SharePoint Enterprise Server 2016, SharePoint Server 2019 or SharePoint Server Subscription Edition should immediately verify whether the January security fixes were applied correctly. That sounds simple, but in practice it means checking the actual build state of production servers, not assuming patch deployment completed as planned.
Security teams should also review whether any SharePoint instances are internet-facing, whether access can be restricted, and whether compensating controls such as segmentation, reverse proxies, application firewalls or temporary exposure reduction are available. Where patching cannot be completed immediately, containment becomes critical.
Log review matters too. If exploitation is active, defenders should not treat this purely as a preventative maintenance task. They should inspect for anomalous requests, suspicious child processes, unexpected changes, unusual web shell indicators, new scheduled tasks, abnormal service behavior and outbound connections that do not fit the server’s usual profile.
Boards and leadership teams should pay attention as well. A collaboration server vulnerability can become a business continuity problem quickly, especially when it touches document workflows, legal records, internal portals or regulated data. The operational cost of delayed remediation can climb fast once compromise moves beyond the initial foothold.
Why this SharePoint flaw deserves sustained attention
There is a reason actively exploited server-side vulnerabilities continue to dominate incident response. They combine reach, speed and consequence. A single exposed server can become the opening move in a much larger breach, especially when it lives inside an environment with broad trust relationships.
CVE-2026-20963 fits that pattern. It affects widely deployed enterprise software, it carries remote code execution risk, and it is now tied to real-world attacks. That is enough to make it one of the more important enterprise patching stories of the week.
For defenders, the takeaway is not complicated. If the vulnerable SharePoint systems are still exposed and unpatched, the window for calm remediation is already closing. At that point, the question is no longer whether the issue is severe. It is whether the organization moved fast enough.
